Introduction to telecom fraud
This guide will help you learn about the different types of telecom fraud and industry best practices for detection and prevention.
Three major categories of telecom fraud
We will divide the many telecom fraud schemes into three broad categories, based on who the fraudsters are targeting. These categories are:
- Traffic Pumping Schemes – These schemes use “access stimulation” techniques to boost traffic to a high cost destination, which then shares the revenue with the fraudster.
- Schemes to Defraud Telecom Service Providers – These schemes are the most complicated, and exploit telecom service providers using SIP trunking, regulatory loopholes, and more.
- Schemes Conducted Over the Telephone – Also known as “Phone Fraud,” this category covers all types of general fraud that are perpetrated over the telephone
Premium rate numbers
Many of the call scenarios featured in this report make use of premium rate numbers. These premium rate numbers are usually to a high cost destination. The owner of the number will offer to share the revenue generated from calls to these numbers with anyone who sends them traffic. This means that a fraudster who generates bogus or stimulated traffic to that destination will receive a kickback for each completed call.
Traffic pumping schemes
The first major category of schemes of telecom fraud is called traffic pumping or access stimulation. These are revenue sharing schemes, characterized by fraudsters whom greatly increase traffic to a specific high cost destination. The destination then shares a portion of their profits with the fraudster.
The call signature for these types of scenarios are spikes in traffic to high cost destinations. Fraudsters often take advantage of lax security practices of a service provider’s customers. A customer whose network has been compromised will often refuse to pay large fraudulent charges, leaving the service provider to cover the bill. Attacks frequently happen over holidays and weekends, when networks are often monitored less closely.
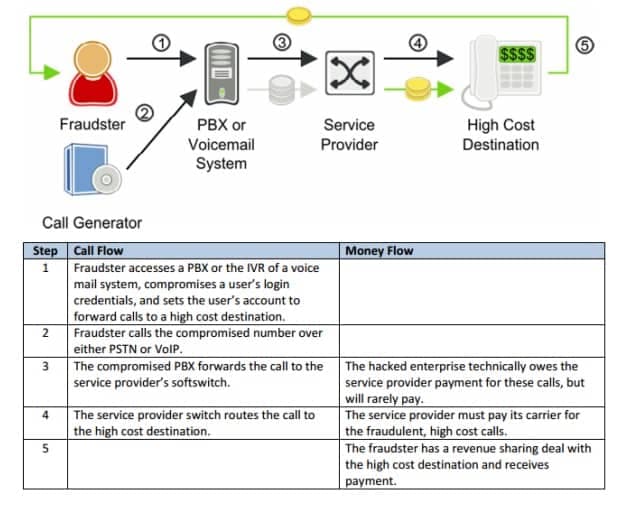
Call forwarding fraud
The Call Forwarding hack is a common form of VoIP telecom fraud. In this case, fraudsters gain access to an enterprise PBX or the IVR of a voice mail system. They can then configure call forwarding to an expensive long distance destination to profit from a revenue sharing deal.
Typically, the service provider’s terms of service clearly state that the customer is liable for fraudulent calls generated from their phone system. In reality, however, few customers ever pay for fraudulent calls and the service provider bears the financial loss because their carrier forces them to pay for fraudulent calls.
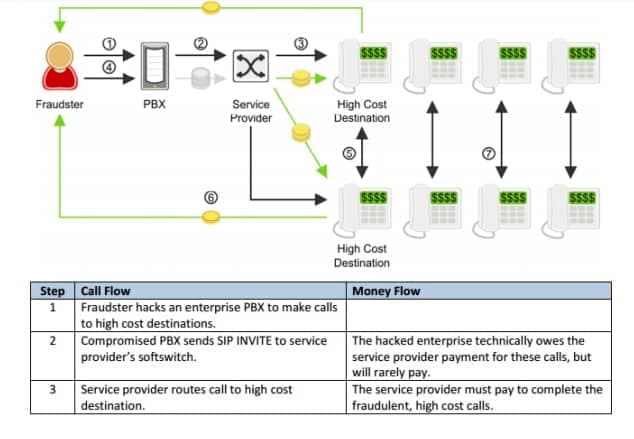
Multiple transfer fraud
Multiple transfer fraud is an enhanced version of the previously described call forwarding fraud. In this fraud scenario, the call is transferred from the call source immediately after the destination answers the call. When the call is transferred, the fraudulent call is in progress with two high cost destinations and the call source hangs up. This fraud technique is especially harmful for several reasons:
- Each fraudulent call results in two call legs to high cost destinations.
- Since the call source is no longer in the call, it becomes more difficult to identify the source of the fraudulent calls.
- The hacked call source can repeat the process rapidly, one call at a time, to setup thousands of concurrent fraudulent calls through the service provider’s softswitch.
Most softswitches limit the maximum number of concurrent calls from a single customer. However, this call transfer fraud technique cannot be controlled by concurrent call limits since the call leg from the hacked phone source and the softswitch is very brief. A hacked customer phone with only a single call channel to a softswitch can generate thousands of concurrent fraudulent calls.
Call transfer is a sophisticated technique for multiplying the effects of telecom fraud, while making the fraud more difficult to detect. Once fraudulent calls are transferred, they stay up until the carrier shuts it down. TransNexus customers report calls staying up for over 24 hours.
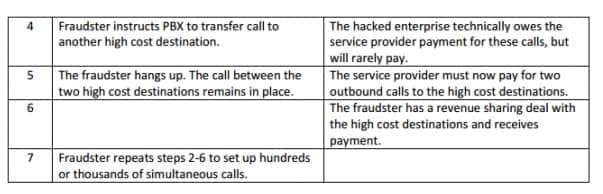
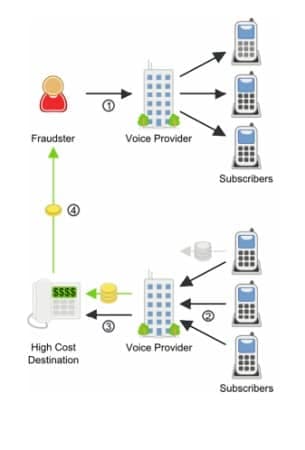
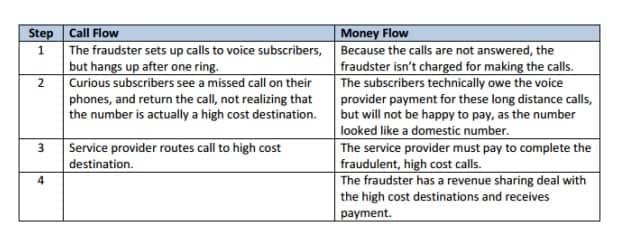
One-ring-and-cut (Wangiri) fraud
Wangiri, in Japanese, means “one and cut.” That is, one ring and a cut off phone call. A wangiri phone fraud scheme relies on this single ring method for a quick way to make money. A fraudster will set up a computer to dial a large number of phone numbers at random. Each rings just once, then hangs up. This leaves a number as a missed call on the recipients’ phone.
Users often see the missed call and believe a legitimate call was cut off, or are simply curious as to who called, so they dial the missed number. This scam is often used to generate calls to Caribbean countries that have the same dial pattern as calls to USA numbers. The number turns out to be a premium rate number – anything from advertising to “free prizes” to sex services.
Schemes to defraud telecom service providers
Telecom Service Providers are particularly vulnerable to telecom fraud. Fraudsters are able to manipulate telecom regulatory systems to their advantage, and to the disadvantage of the service provider, in ways that are difficult to detect, trace, and prosecute.
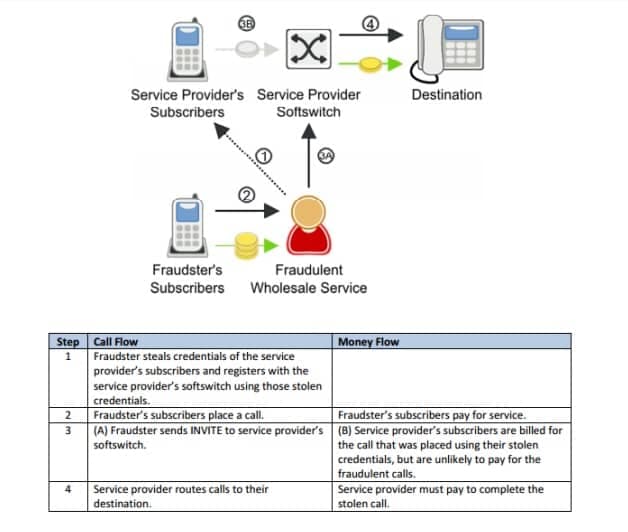
Wholesale SIP trunking fraud
Fraudulent wholesale trunking is a relatively new phenomenon, but one that is growing in popularity and difficult to detect. In this scenario, the fraudster is actually making money by selling wholesale trunking services, using stolen credentials to terminate the calls. The key calling signature for this type of fraud is an increased number of apparently random calls. The destinations are not particularly high cost, but neither are they cheap. Countries like Vietnam, Laos, and other middle-priced Asian countries show up often. The traffic often appears to be to residential numbers.
TransNexus customers have reported tracing this type of fraudulent traffic coming from prepaid calling card companies operating a VoIP platform in an offshore colocation facility. Prepaid calling services are well suited to exploit this type of fraud since there are no calling numbers linked to customers. The IP address of the prepaid calling platform is the only link to trace the fraudster. Unfortunately, geolocation cannot always be used to identify the fraudster. These services can be offered via a tunnel through the Internet that hides the true IP address of the fraudster. The public IP address of the fraudster’s calling platform could be the IP address of a hosted Virtual Private Network (VPN) service while the actual prepaid calling platform is located in a different part of the world.
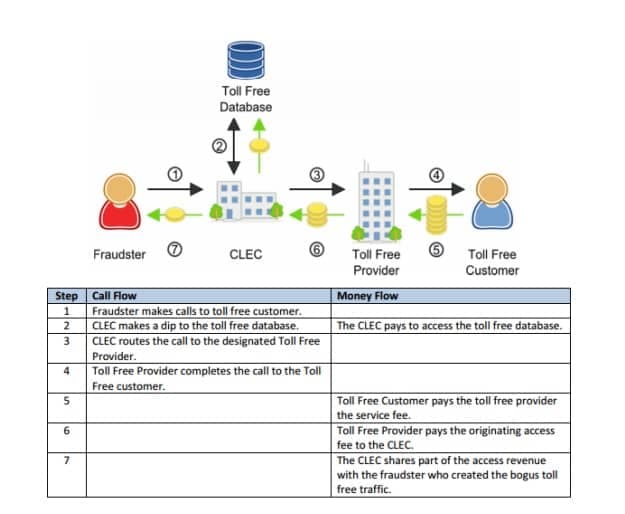
Toll free fraud
Toll Free fraud can affect any business that uses a toll-free number. These calls are often left up for hours at a time and automated so multiple calls will be made at once. Fraudsters have gotten very sophisticated with this style of fraud, using different calling numbers for each call and only calling during business hours. They can navigate the IVR system to maintain a call for long periods of time, and vary the call duration so that the calls appear to be real traffic. When large companies, like financial institutions, are targeted, they frequently don’t even notice the huge charges racked up by toll free fraud, even though they are expensive, long calls.
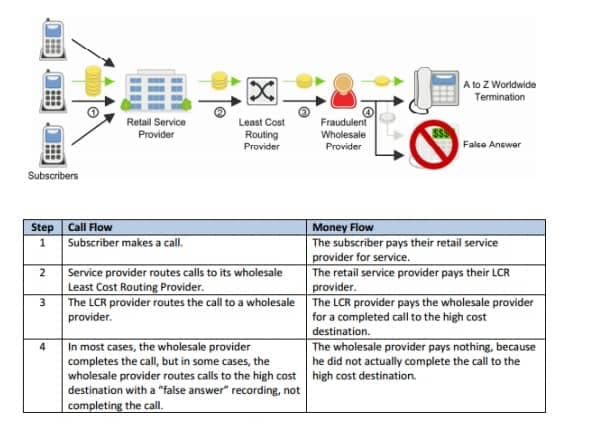
False answer supervision
When a dialed phone number is not in service, the calling party will hear a brief recording telling them so. There is no answer supervision or connection between the calling and called party. Since the call never connects, it is an incomplete call and should not be billed. However, fraudsters use false answer supervision to make these calls appear as completed calls which may be billed. Perhaps the fraudster has published rates for terminating calls without any intention of actually completing the calls. Here, service providers will route calls through the fraudster, who, instead of terminating the call, will play a not in service message and then bill the service provider for more than 10 seconds of calling. This type of fraud hurts the originating service provider both by costing money, and by hurting their reputation.
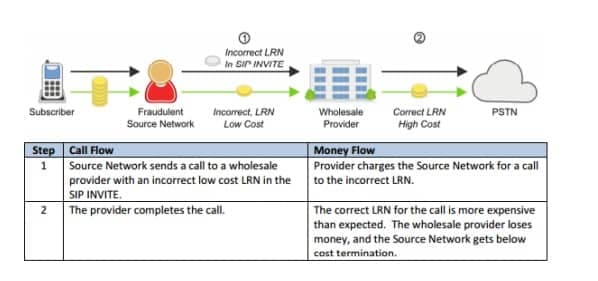
Location routing number fraud
Location Routing Number Fraud (LRN) fraud works based on the desire of some service providers to avoid extra charges from LRN “dips.” Most providers will run an LRN dip to determine the correct LRN for a dialed number. However, some service providers will not perform an LRN dip if the LRN is already in the SIP message. Fraudsters take advantage of this by inserting the LRN for a relatively cheap terminating destination in their SIP INVITES, when the call is actually going to a high cost rural destination. The service provider will route and bill the fraudster using the LRN included in the SIP INVITE. The network that provides PSTN termination will route and bill for the call to the high cost rural destination using the correct LRN. The service provider will under-bill its customer for the call and will have to pay for the cost of the expensive rural call. In some cases, this can be up to 5x the price they billed the fraudster.
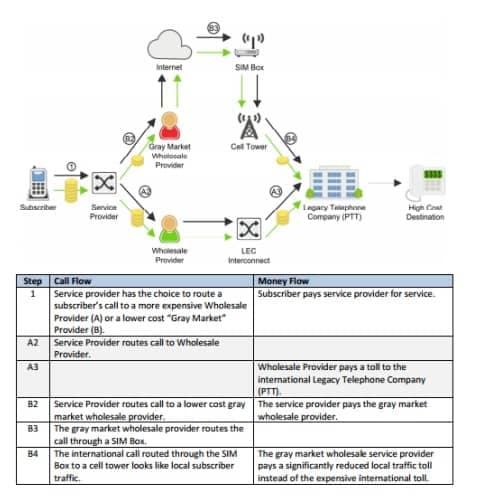
Toll bypass fraud
Bypass fraud is the unauthorized insertion of traffic onto another carrier’s network. In many countries, toll bypass for international call termination is criminal fraud. This scenario requires that the fraudsters obtain network access which makes international calls appear to be cheaper, domestic calls, effectively “bypassing” the normal payment system for international calling. One common technique for perpetrating this Interconnect fraud is GSM Gateway fraud, or SIM Boxing which is illustrated in the following diagram.
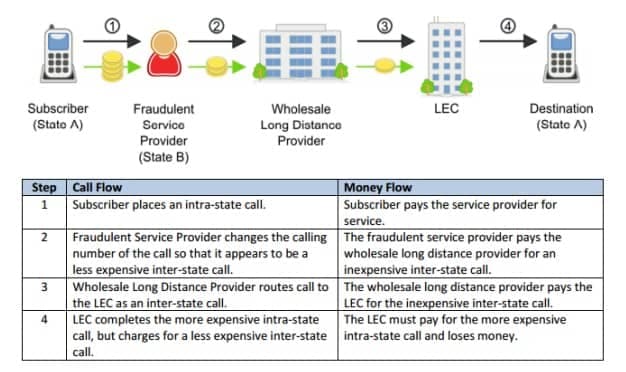
Inter/intrastate tariff bypass fraud
Bypass fraud is the unauthorized insertion of traffic onto another carrier’s network. Inter/intrastate toll bypass fraud attempts to bypass the higher tolls of intrastate traffic by making it look like interstate traffic.
Schemes conducted over the telephone
Criminals of all sorts use telephony as a tool to defraud consumers and businesses. “Phone fraud” is a huge category, and can cover anything from Nigerian prince style scams to identity theft to extortion. TransNexus does not offer a solution to protect against these types of fraud, though there are other solutions on the market that can.
Account takeover
With this type of telecom fraud, the fraudster generally attacks something like a financial institution Fraudsters will call financial institutions and maliciously impersonate another customer in order to steal the contents of an account. Pindrop Security estimates that a financial institution taking 50,000 calls per day will lose over $10 million per year to phone fraud losses.
Telecom denial of service (TDoS)
Telecom Denial of Service (TDoS) attacks are similar to traditional data network denial of service (DDoS) attacks. In a DDoS attack, unauthorized users flood a system with too many access requests, preventing legitimate users from accessing the network. For TDoS, fraudsters make a huge number of phone calls, keeping them up for long durations, and overwhelming the capacity of an organization’s phone network. TDoS attacks can impair a voice network’s availability, but can also be used as a tool for extortion. TDoS attacks have been in the news recently as a threat to public safety, as fraudsters have taken to using TDoS attacks against hospitals, police stations, and other public services.
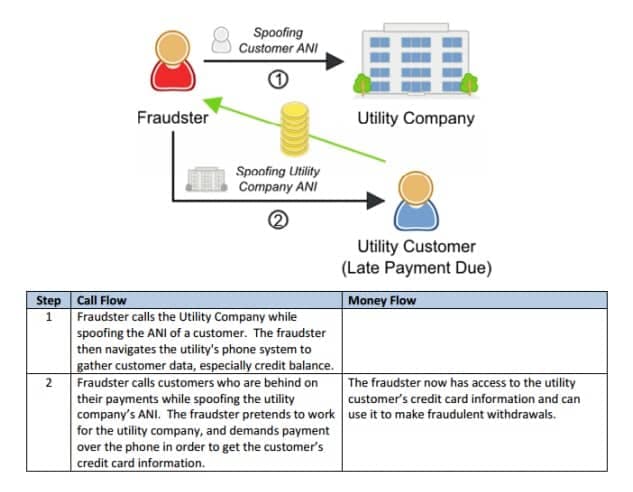
Vishing
Phishing is a form of fraud that uses email messages with phony addresses, websites or pop-up windows to gather your personal information, which can then be used for identity theft. A form of phishing that uses the telephone instead of email is known as Vishing or “Voice-Phishing.” Vishers pose as a legitimate business to attempt to gather information from someone. That information can then be used for identity theft or other forms of fraud.
TransNexus telecom fraud prevention solutions
TransNexus solutions effectively eliminate the problems of traffic pumping fraud, PBX hacking, revenue sharing fraud, blind transfers, and call forwarding fraud for VoIP providers. The solution is to include smart monitoring that measures financial risk in near real time by Source IP, Calling Number, Customer ID, and by Detailed Dial Codes (country, state, mobile). TransNexus solutions send alerts or block calls when financial risk exceeds historical norms. TransNexus fraud detection features also include fraud blacklists, call diversion, and call blocking.
Summary
VoIP fraud is, and will remain, a lucrative criminal business. As VoIP continues to grow in popularity, schemes for beating the system will continue to become more complex and powerful. VoIP providers and enterprises must work together to ensure their networks are secure from every angle. By securing networks and analyzing traffic for signs of fraud, VoIP providers can minimize their fraud risks.
More on TransNexus.com
February 15, 2023
Suggestions to curb access arbitrage
June 27, 2022
FCC proposes new rules to prevent access stimulation
June 6, 2022
Denial of service attack and ransom demand defeated
May 18, 2022
China cracks down on telecom fraud
December 6, 2021
Telecom fraud losses increasing, according to CFCA report
December 1, 2020
FCC Report and Order on one-ring scam calls
November 9, 2020
Domestic telecom toll fraud is still a problem
October 12, 2020
FCC changes rules for intercarrier compensation on toll free calls
January 23, 2020
TRACED Act calls for one-ring scam protection
November 19, 2019
Robocall and TDoS case studies
October 28, 2019
FCC denies stay request on their Access Arbitrage Order
October 28, 2019
Wangiri telecom fraud activity reported in Canada
September 26, 2019
FCC issues order to prevent access stimulation
July 16, 2019
ClearIP adds new call forwarding blacklist capabilities
July 10, 2019
July holiday week telecom fraud attack profiles
June 13, 2019
ClearIP enhancements for blacklisting of SPID and location
May 20, 2019
Anatomy of a telecom fraud attack
May 14, 2019
Study on rule changes to eliminate access arbitrage
May 8, 2019
FCC warns of Wangiri telecom fraud scams
March 8, 2019
SIP Analytics vs. CDR-based fraud management – a case study
October 22, 2018
FCC proposal to curb domestic telecom fraud
September 27, 2018