Robocall and TDoS case studies
November 17-23, 2019 is International Fraud Awareness Week. The Communications Fraud Control Association (CFCA) has encouraged members to share information so we can work together to combat it. So, we’re sharing three case studies of a series of domestic telecom robocalls and TDoS attacks we observed just last month, in October 2019. Here’s what happened.
Case One: A business in Texas
This business was the target of 71 fraud attacks comprised of about 3,000 calls. These attacks were defeated by our ClearIP software using SIP Analytics and Phone Number Reputation Lookup.
But before we get into all of that, you might be wondering, why would a fraudster call a business in Texas? Telecom fraud usually involves high-cost destinations, and that doesn’t sound like a high cost destination.
And you would be correct. This was not a high cost destination.
We found that these calls were from several alleged calling numbers. They weren’t signed using STIR/SHAKEN, so some of the calling numbers may have been spoofed.
Almost 300 of these calls had a poor reputation and were blocked by our Phone Number Reputation Lookup. These were from known robocallers selling things like health insurance and, this being Texas, oil and gas investment opportunities.
In retrospect, this isn’t surprising. October was reported to have been the highest month yet for robocalls. The count was boosted by a flurry of spam calls pitching health insurance in the lead up to open enrollment season.
So, many of these attacks were not intended to defraud—they were from a spammer trying to sell. But that doesn’t tell the whole story.
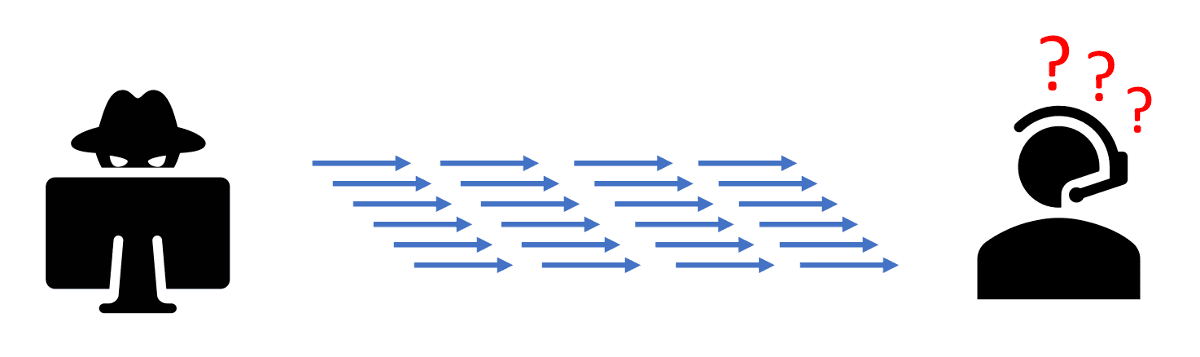
Of the remaining calls, some of these attacks targeted this business’s toll-free number. These calls came in bursts about one second apart. These seem to have been a TDoS (Telephony Denial of Service) attack.
We’ve noticed an uptick in the number of businesses being targeted by TDoS attacks. The calls are intended to tie up customer service reps with nuisance calls so they can’t answer real calls. Frustrated customers can’t get through, so they give up and call someone else.
It’s modern warfare on the business battlefield.
Case 2: A travel business
This business does most of their selling online, but they also receive a lot of telephone calls from their customers. They’ve had problems with inbound calls tying up their customer service representatives so they can’t take care of real customers.
This company was targeted with over 700 attacks in October consisting of over 8,000 calls. A classic TDoS attack.
SIP Analytics detected and blocked these attacks, and the company was able to take care of its customers.
Case 3: An auto dealer
An auto dealer receives a flurry of calls that tie up their phones. Operators were at their wit’s end. The company struggled to take care of its customers.
In October, they were targeted by 3,000 calls. Another TDoS situation.
As with the other cases, ClearIP blocked the attacks while normal business calls continued.
Lessons learned
We think the takeaways from these case studies are as follows:
- Robocalls can be more than just a nuisance—they can shut down a business’s ability to serve its customers.
- Robocall perpetrators sometimes send so many calls that they shut down business communications—whether intended, or not, it’s TDoS.
- TDoS is on the rise, and it’s being used as a competitive weapon.
- Call analytics can prevent these attacks and protect your telephone service.
- STIR/SHAKEN can’t come soon enough. It would help identify spoofing and traceback, a valuable defense against such attacks.
Contact us today to learn how we can protect your business customers from robocalls and TDoS attacks.
