STI Governance Authority changes SPC policy start date
The STI Governance Authority yesterday announced a change in the effective date for their new SPC token access policy. This will make it easier for some service providers to certify either complete or partial SHAKEN implementation in their robocall mitigation filing. Here are the details.
Background
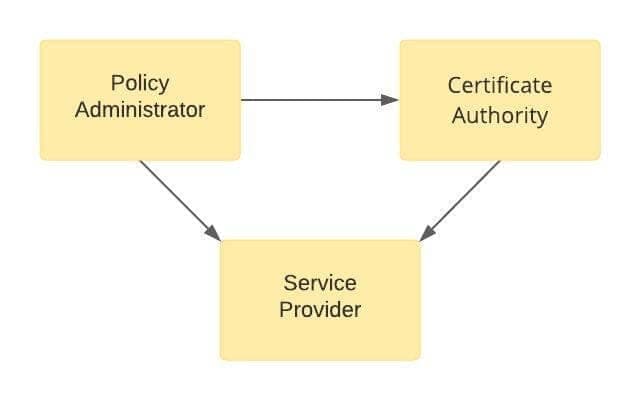
Only authorized voice service providers are allowed to obtain SHAKEN certificates from Certificate Authorities so they can sign calls with STIR/SHAKEN. This establishes a triangle of trust between authorized participants which ensures that (1) bad actors cannot participate, and (2) signed calls can be trusted.
Triangle of Trust
The STI Governance Authority (STI-GA) sets policies which other participants must follow. The initial policy for service provider eligibility required the following from participating service providers:
- 499-A filing
- OCN
- Access to numbering resources.
The third criteria is a stumbling block for many voice service providers that offer telephone numbers from DID providers but do not have access to numbering resources themselves. They cannot qualify for SHAKEN certificates under this policy and cannot participate in the SHAKEN ecosystem.

Policy change
The STI-GA announced a change to this policy on November 18, 2020. The third criteria would be changed to a requirement that service providers must have certified with the FCC that they have implemented STIR/SHAKEN and/or have a robocall mitigation program.
This policy was initially set to take effect when the FCC launched its Robocall Mitigation Database portal sometime around April 2021. However, in their 2020 Year-End STI-GA Report published February 4, 2021, the GA stated that “registration in that database will replace the telephone number access requirement as the third authorization prong no earlier than June 30, 2021.”
This created a timing problem: some service providers cannot qualify for an SPC token until the policy change takes effect. However, the policy change was now set to take effect on the same day as the robocall mitigation certification filing deadline.
Change in effective date
On May 10, 2021, the GA announced that the new policy is effective immediately. The third criteria, certification filed with the FCC and listed in the Robocall Mitigation Database, is now available for service providers to qualify for an SPC token.
The current policy, which requires access to numbering resources, will continue to remain in effect until June 30, 2021. This means that service providers that qualify for SPC tokens will continue to be qualified until that date. After that, they have to qualify under the new requirements.
IMPORTANT NOTE: Service providers that obtained SPC tokens under the current policy must meet the revised criteria within 30 days of the FCC certification filing deadline. Any provider that has not certified with the FCC by July 30, 2021, risks having its SPC token revoked.
Implications
- Many service providers can now qualify for SHAKEN tokens under the new policy. They just have to file a certification ASAP.
- This may enable some service providers to qualify for a complete SHAKEN implementation filing, which means they do not have to deploy a robocall mitigation program.
- Some providers may qualify for partial SHAKEN implementation filing. They still have to deploy a robocall mitigation program, but not for calls they originate and sign with SHAKEN.
TransNexus solutions
We offer STIR/SHAKEN and robocall mitigation solutions in our ClearIP and NexOSS software platforms.
In addition, we help service providers with all aspects of STIR/SHAKEN deployment, including registering with the Policy Administrator and filing their Robocall Mitigation certification with the FCC.
Contact us today to learn more.
Our STIR/SHAKEN products:
- Work with your existing network
- Support SIP and TDM
- Affordable, easy to deploy